What is the ISO 27001?
The ISO 27001 standard was defined by the International Organization for Standardization (ISO) and developed particularly for information security management. It specifies requirements for an information security management system (ISMS) that helps to increase information security in companies. High information security means that the information security objectives are achieved. These are
- Confidentiality,
- integrity and
- availability of information
ISO 27001 includes a systematic and proactive approach to identifying, assessing and managing information security risks. The practices and controls help to identify and close security gaps in order to minimize potential security incidents. ISO 27001 provides a framework for the development, implementation, monitoring and continuous improvement of an ISMS.
What is an ISMS and why is it important for ISO 27001?
An information security management system is a structured and holistic framework. It comprises guidelines, procedures, processes and technical controls aimed at protecting the confidentiality, integrity and availability of information (= objectives of information security).
The ISMS is crucial to the implementation of the ISO 27001 standard as it provides the framework within which the requirements of the standard can be met. By implementing an ISMS, companies can ensure that their information security practices are systematically developed, implemented, monitored and improved, which in turn contributes to meeting the ISO 27001 requirements.
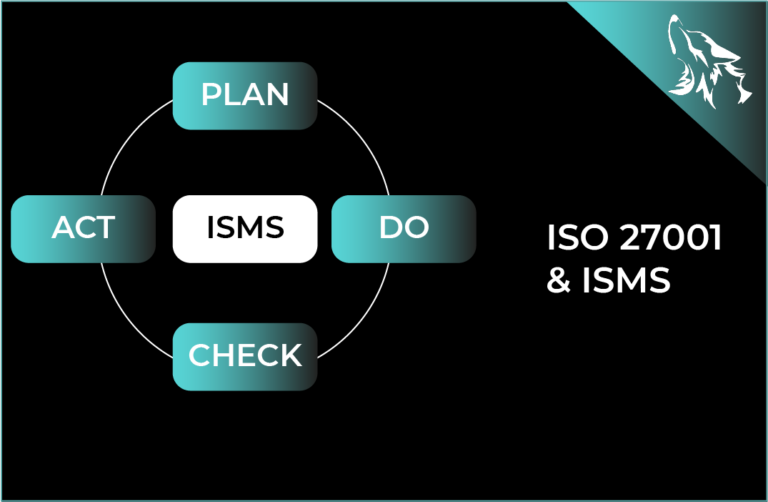
An ISMS is generally based on the PDCA cycle (Plan – Do – Check – Act), which enables continuous improvement of the information security level.
What is the PDCA Cycle?
The PDCA cycle (Plan-Do-Check-Act) is a well-established model for continuous improvement that is often used as part of quality and management standards. The phases of the PDCA cycle are as follows:

- Plan: Definition of objectives and processes to achieve these objectives, including the identification of risks and opportunities.
- Do: Implementation of the planned processes and procedures in accordance with the defined objectives and guidelines.
- Check: Monitoring and reviewing results and processes to ensure that they meet expectations and that the defined objectives are achieved.
- Act: Implementation of measures to ensure continuous improvement based on the review results, including the adaptation of processes and measures to increase effectiveness and efficiency.
The PDCA cycle enables companies to continuously improve their performance by systematically setting, implementing, reviewing and adjusting targets.
How is an ISMS set up?
The main components of an ISMS include:
- Risk assessment and treatment: This refers to the identification of information security risks, the assessment of their impact and the likelihood and implementation of risk mitigation measures.
- Policies and procedures: Development of policies and procedures to control and monitor information security activities.
- Employee security:: Implementation of measures to ensure that employees are adequately trained and comply with the company's security policies and procedures.
- Physical security: Protection of the physical environment in which information is stored and processed against unauthorized access, theft or damage.
- Technical security: Implementation of technical controls and mechanisms to secure information systems and infrastructures.
Implementing an ISMS in accordance with the requirements of ISO 27001 helps to strengthen the trust of customers, partners and other stakeholders in your company. ISO 27001 and a well-structured ISMS are therefore essential components for companies that want to ensure that their information is adequately protected and meets data protection, compliance and security requirements. They also actively protect themselves against potential threats.
How does a company set up an ISMS?
The development of an ISMS requires a systematic method based on the company’s individual requirements and risks. A typical procedure includes the following steps:
- Initiation and commitment: The company's management must commit to implementing an ISMS and provide the necessary resources. An ISMS is a management responsibility!
- Definition of the scope: The scope of the ISMS must then be defined, including the information to be protected and the relevant legal and regulatory requirements.
- Risk assessment: This is followed by the identification and assessment of information security risks that could affect the company.
- Development of policies and procedures: Next, policies, procedures and processes are created to control and monitor information security activities.
- Implementation of controls: As part of this step, technical and organizational controls are introduced to secure information systems and infrastructures.
- Training and awareness: A very important step is to train employees on information security policies and procedures and to raise awareness of security risks and measures.
- Monitoring and review: Regular monitoring, review and evaluation of the ISMS is key to ensuring that it is effective and meets changing requirements. The ISMS is therefore never "finished", but is constantly changing in order to improve.
- Continuous improvement: Improving the ISMS is achieved by identifying and implementing appropriate measures.
Steps 7 and 8 correspond to the Check and Act steps in the PDCA cycle.
Our experts support you on your way to ISO 27001 certification or any other desired certification such as TISAX® certification, ISO 21434, ISO 9001, etc.
We support you from the preparation to the audit and can also take over communication with the certification body/auditor on request.

How to obtain ISO 27001 certification?
The ISO 27001 certification audit is carried out by independent certification bodies that check the conformity of a company with the requirements of the ISO 27001 standard. The certification process usually comprises the following steps:
- Preparation: The company prepares for certification by implementing an ISMS in accordance with the requirements of ISO 27001.
- Internal review: The company carries out an internal review of the ISMS to ensure that it meets the requirements of the standard.
- Selection of a certification body: The company selects an accredited certification body that will carry out the certification, for example TÜV Nord.
- Certification audit: The certification body conducts an initial certification audit.
- Certification decision: Based on the results of the audit, the certification body decides whether the ISMS will be certified.
- Surveillance audits: After certification, the certification body conducts regular surveillance audits to ensure that the ISMS continues to meet the requirements of the standard.
ISO 27001 involves an annual review audit and a recertification audit every 3 years by an external audit service provider.
What are the ISO 27001 requirements for certification?
ISO 27001 specifies a number of requirements that companies must fulfill in order to be certified. The most important requirements include
- Defining the scope of the ISMS: Defining the scope of the ISMS, including the information to be protected and the relevant legal and regulatory requirements.
- Risk assessment and treatment: Identifying and assessing information security risks and implementing risk mitigation measures.
- Policy and procedure development: Creating policies, procedures and processes to control and monitor information security activities.
- Implementation of controls: Introduction of technical and organizational controls to safeguard
What are the benefits of ISO 27001 certification?
ISO 27001 certification can help companies gain the trust of their customers and other stakeholders as it demonstrates that the company has implemented appropriate security measures to protect its own information and that of its supply chain. As ISO 27001 is internationally recognized, it is also recognized worldwide as a “proof of trust”.
The key benefits include:
- Improved security level: By implementing an ISMS in accordance with the requirements of ISO 27001, companies can improve their information security level and protect themselves better and, above all, proactively against security incidents.
- Risk management: ISO 27001 requires systematic identification, assessment and treatment of information security risks, which helps to minimize potential security threats.
- Basis for further standards: The ISMS is a good basis for implementing further standards, such as TISAX®, as your company already has a certain information security standard with the ISMS.
- Compliance with legal and regulatory requirements: ISO 27001 provides a framework for meeting legal and regulatory requirements in the area of information security and minimizing compliance risks.
- Gaining trust: ISO 27001 certification is a sign of a company's commitment to information security and can strengthen the trust of customers, partners and other stakeholders.
- Competitive advantage: ISO 27001 certification can serve as a differentiating feature compared to competitors and helps to open up new business opportunities.
- Continuous improvement: ISO 27001 requires continuous monitoring, review and improvement of the ISMS, which helps to increase the effectiveness and efficiency of information security practices over time.
- Cost savings: A well-implemented ISMS can help to reduce the costs associated with security incidents and enable more efficient business processes.
Automated solutions, such as NORM X, can save both costs and time.
With our NORM X solution, you ensure a fast and efficient journey to ISO 27001 certification. With over 40 years of expertise and the IX Certification Engine, NORM X puts you in the fast lane to your goal:
- Low start-up and follow-up costs allow up to 50% TCO savings.
- Get everything from a single source. No other resources are needed.
- Up to 6 months time savings through automated process flows.
Summary
ISO 27001 and the information security management system (ISMS) play a crucial role in ensuring information security in companies. By implementing an ISMS in accordance with the requirements of ISO 27001, organizations can proactively identify, assess and address security risks to adequately protect their information.
ISO 27001 certification offers a wide range of benefits, including improved security, risk mitigation, compliance with legal requirements and gaining the trust of customers and partners. By continuously monitoring, reviewing and improving the ISMS, companies can ensure that their information security practices meet changing requirements and thus make an important contribution to the long-term success of the company.